Generating API Keys
You can gain access to your Optimove data and trigger actions within Optimove via API. To enable an efficient and secure process, API requests are authenticated using API Keys.
An API key is a code that is passed in by computer programs calling an API to identify the calling program and to provide access to the resources that the caller is authorized to use. The key acts as a secret code that is used to identify the user, application, or developer. It is also known as an API token.
API Keys ensure maximum security and only provide authorized applications access to the resources. By using API keys, we can easily revoke access to a specific application without impacting other applications.
Using an API Key does not require a preliminary request to the /login endpoint. By embedding the key in the request header, the user is “always logged in”.
If you are a third party collaborating with us, we kindly request the client you're assisting to generate a key for your use.
How to Generate an API Key
- As an admin user, go to the Settings page
- Under General, go to API Key Management
- Click the “+ New API Key” button

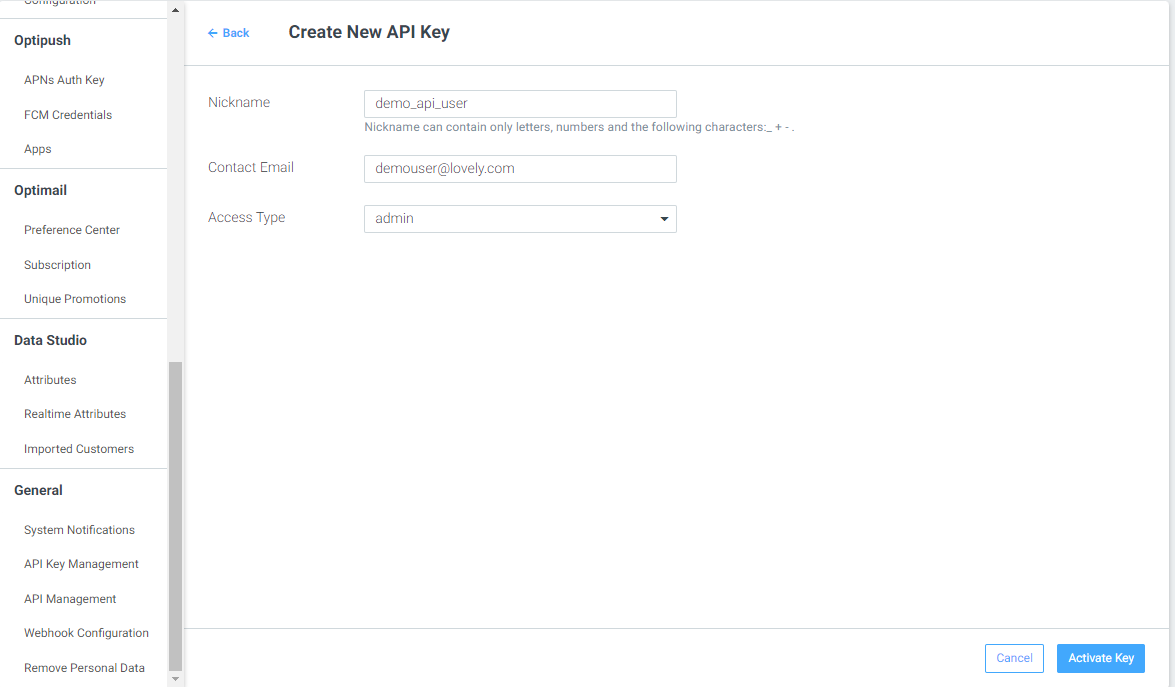
- Select a “Nickname” - an identifiable name easy to connect to the it’s actual user.
- Fill in your Contact Email
- Select an Access Type:
- Select Admin for API full permitted user.
- Select Integrations for channel integration purposes.
- Click on “Activate key”
- You will then be provided with a unique API key that will be used for authentication purposes.
Please note
API keys should be stored securely. We should never hard-code the API key in the application code or store it in plain text. It is recommended to use a secure key-value store like HashiCorp Vault or AWS Secrets Manager to store the API key.
For more information on API Keys, refer to the Authentication Guide.
Access Types
There are three options for Access Type:
-
Admin
- A full permitted user, permitted to access any of the API calls and all of Optimove’s API available functions
-
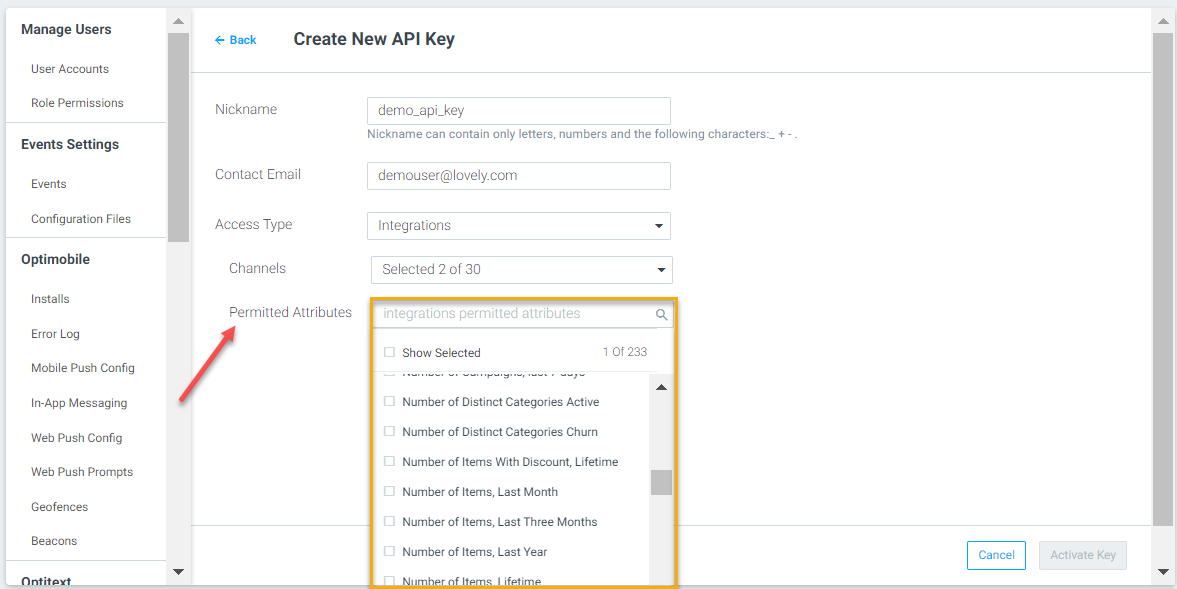
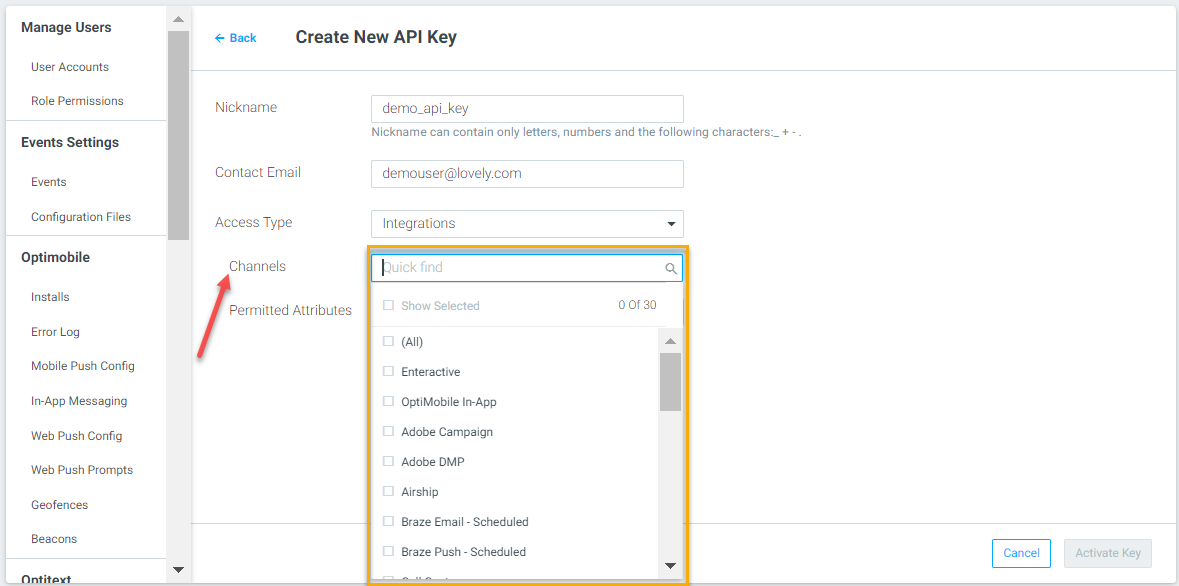
Integrations - for 3rd Party User
-
Third-party keys are limited in access permissions.
-
Only a part of the API calls are available. You can find the list here.
-
Within the available ones, only certain attributes can be limited to be shared with the 3rd Party provider.
-
Additionally, only specific channels can be enabled to a certain CID.
-
For both limitations, if none is selected, all channels are permitted.
-
-
Transactional API User
- The "Transactional" user role provides access to all endpoints, including the "transactional" functionality.
- Users with this role can utilize the full range of API endpoints, including those related to transactional operations.
- Please ensure that users are assigned the appropriate roles and permissions based on their intended usage and the level of access required.
Best Practices for using an API Key
- Use a different API key for each application.
- Regenerate API keys periodically.
- Never share API keys on public platforms like GitHub.
- Use HTTPS to transmit API keys.
- Set up rate limits to control the usage of API keys.
- Monitor API key usage regularly.
By following these best practices, we can ensure the security of our APIs and prevent unauthorized access to our resources.
Please use your API key ONLY for production purposes. All uses of this key will affect your production site.
Updated 7 months ago
